A Year of Proof: Why Prevention is the Only Path Forward
As we close the chapter on 2025, we find ourselves reflecting on a year shaped by three powerful forces: curiosity that pushed boundaries, relentless execution that turned ideas into impact, and, above all, operational proof that our approach works.

At Aryon Security, this was a year to celebrate. We started with a straightforward yet disruptive belief: proactively preventing misconfigurations at the source scales far better than cleaning them up after the fact. In today's sprawling, multi-cloud world, the old "detect-and-remediate" playbook has reached its breaking point.Organizations are drowning in alerts, racing against attackers who move in minutes, and burning through engineering hours on fixes that shouldn't have happened in the first place. This year demonstrated that cloud security without paralyzing engineering is the only sustainable model.
The Strategic Perspective (Joshua Behar):
"Having led global security organizations through the evolution of cloud and edge computing, I’ve seen firsthand the fatigue that sets in when 'Detection' is the only tool in the shed. You cannot build a resilient enterprise on a foundation of constant firefighting. As a strategic advisor, my focus with Aryon this year was validating that 'Prevention-First' isn't just a technical achievement, it is a business imperative for the modern CISO. Our 2025 results prove that we have finally closed the gap between security intent and operational reality."
We are immensely proud of our team for transforming that bold vision into a working reality. And we are deeply thankful to our investors: Viola Ventures, Blumberg Capital, and ourremarkable angels, who backed us when this was still just a compelling idea. Together, we've demonstrated that shifting security controls closer to the point of deployment isn't merely advantageous, it's essential for any business serious about thriving in the cloud era.
The Silent Epidemic: The Harsh Reality of Today's Cloud Security
To appreciate why 2025 marked such a turning point for Aryon, consider the bigger picture. For years, Gartner has delivered a stark warning that has become the industry’s grim benchmark: through 2027, 99% of records compromised in cloud environments will be the result of customer misconfigurations, not attacker sophistication (Gartner, 2023).
This isn't about blaming cloud engineers or DevOps teams, they're talented professionals navigating unprecedented complexity. It's about the limitations of the tools and processes they've relied on. As companies raced through digital transformations, they inherited an unmanaged attack surface that grows faster than anyone can monitor.
The vast majority of these incidents trace back to preventable misconfigurations: an S3 bucket left public during a rushed deployment, overly permissive IAM roles set to "fix" an urgent issue, or a legacy firewall rule carried over from on-prem days. We've spent the better part of a decade building ever-more sophisticated detection tools CSPMs, vulnerability scanners, threat hunters, yet breaches continue at an alarming pace.
Why? Because the industry has been stuck in a reactive cycle. A well-meaning engineer tweaks a setting in the console at 2 a.m. A script deploys with a tiny oversight. Shadow IT spins up resources outside approved channels. By the time detection kicks in, the exposure is live, and the race to remediate begins. Attackers don't wait for tickets or approvals, they exploit in moments.
Why "Shift-Left" Fell Short in the Real World
Early this decade,"Shift-Left" security captured the spotlight and for good reason. The concept was elegant: catch issues early in the development lifecycle, before they reach production. Scan IaC templates, enforce checks in CI/CD pipelines, integrate security into developer workflows.
It worked wonders for teams with mature, automated pipelines. But 2025 laid bare its limits in the messy reality of enterprise environments.
Most cloud changes don't neatly flow through a pristine pipeline.
Consider the everyday chaos:
● Infrastructure as Code scripts that grow so complex even the best scanners miss subtle risks.
● "ClickOps" during outages: someone logs into the AWS, Azure, or GCP console and manually adjusts resources to keep services running.
● Third-party tools and integrations that quietly provision resources beyond visibility.
● Legacy migrations where old, insecure settings hitch a ride into the cloud.
These bypass "shift-left" entirely. That's why detection-focused tools exploded in popularity, they shine a light on the aftermath. But shining a light doesn't prevent the fire. Mean Time to Remediation (MTTR) for misconfigurations often stretches to days or weeks, while an exposed asset can be compromised in minutes. The gap between discovery and action remains the attacker's biggest ally.
The Aryon Breakthrough: Turning Prevention into a Scalable Platform
In 2025, we set out to close that gap once and for all. Our mission: evolve cloud security from a visibility-and-alerts function into true enforcement at the point of change.
We built the Aryon Enforcement Layer to serve as that final, proactive reliable gatekeeper. No matter how a change arrives, through Terraform, a CLI command, a console click, or an automated tool, if it violates security policy, it's flagged or blocked before it ever impacts the live environment. This is how to prevent cloud misconfigurations in AWS/Azure/GCP effectively.
What makes this possible at enterprise scale? Our Adaptive Policy Engine. It goes beyond rigid, static rules. It draws from established standards like CIS Benchmarks and NIST, but layers in contextual intelligence to align with each organization's unique risk profile, compliance needs, and operational realities.
The biggest hurdle we overcame this year? Ensuring prevention doesn't paralyze productivity. Security leaders often hesitate to enable blocking mode, fearing they'll halt critical business work. We addressed this head-on with Policy Impact Assessment: team scan simulate enforcement, preview exactly what would be stopped, and fine-tune policies with confidence before going live. The result? Prevention that empowers rather than obstructs.
2025 by the Numbers: Real Impact, Real Proof
Pride without proof is just optimism.
Massive ROI: Saving $41.4M with Proactive Prevention
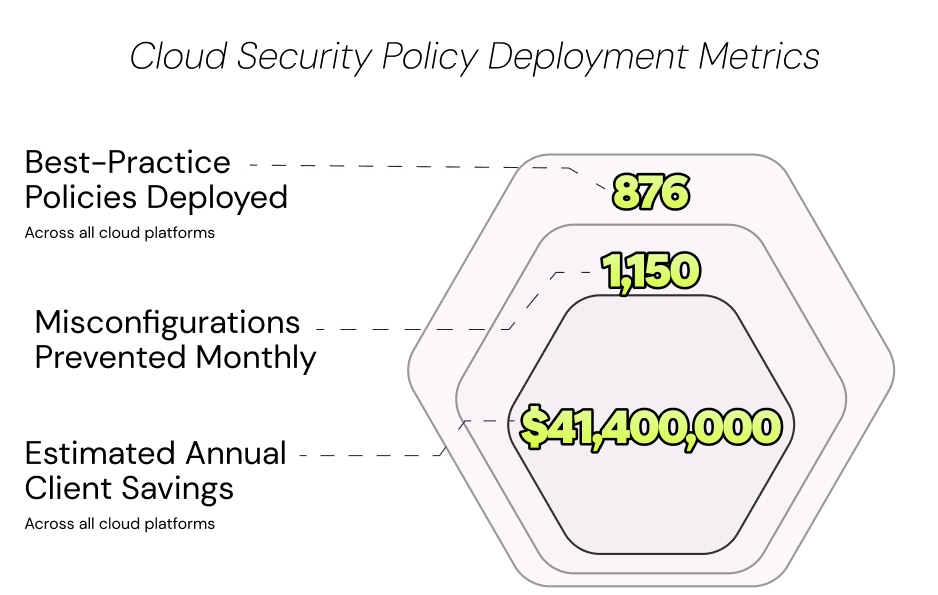
Here are selected metrics from our deployments that tell the real story:
● 876 Best-Practice and Custom Policies Deployed: We went far beyond generic templates, delivering nearly 900 finely tuned policies tailored across AWS, Azure, and GCP, granular protection that manual processes could never sustain.
● 1,150 Misconfigurations Prevented Monthly: This is the metric that defines the platform’s value. Each prevented incident means noexposure ever went live. No frantic alert. No remediation ticket. No engineerpulled into a war room weeks later to undo a forgotten mistake. Pure, silent risk reduction.
● $41,400,000 in Estimated Annual Client Savings: Prevention delivers measurable ROI. Each misconfiguration carries an estimated true cost of $2,795–$4,075, covering SOC triage, engineering remediation, tooling, downtime risk, statistical breach exposure, and compliance overhead (IBM Cost of a Data Breach 2025; BLS 2024; Verizon DBIR 2025). Consider also the worst-case: a breach with global averages around $4.44 million per incident in2025, and over $10 million in highly regulated U.S. environments. By stopping issues upstream, our customers reclaim budgets and focus on innovation insteadof firefighting.
A Personal Note of Gratitude
Numbers matter, but people make them happen. To the Aryon team: you are the heartbeat of this company. You embraced the prevention philosophy and translated it into technology that safeguards some of the world's most sophisticated infrastructures. Your refusal to settle for "another dashboard" drove us forward.
To our investors, Viola Ventures, Blumberg Capital, and remarkable angels like Shlomo Kramer, Maty Siman, Rubi Aronashvili, and others, thank you for betting on us early. Your belief turned vision into velocity.
Looking Ahead: Keeping Prevention at the Forefront
2025 proved prevention isn't a trend, it's the new standard. The conversation has shifted from" How do we spot risks?" to "How do we make sure they never materialize?"
We won't spill the full 2026 roadmap here (competitors read these too….), but know this: we're just getting started. The cloud's complexity will only intensify with AI-driven workloads, sovereign cloud mandates, edge expansions, and more. Our commitment remains laser-focused: innovate at the point where actions happen, building an adaptive guardrail and an enforcement layer that evolves with threats and organizations alike.
We're not just delivering a security platform. We're engineering the immune system the cloud as always needed, one that anticipates, protects, and enables without compromise.
Here's to 2026 and beyond. The best proof is yet to come.
Ron Arbel (רון ארבל)
CEO, Aryon Security


Got Questions? We've Got Answers!
If you don't find the answer you're looking for here, feel free to reach out to us here.
How is Aryon different from a CSPM tool?
CSPMs operate after deployment, they scan your live environment, identify what's misconfigured, and generate alerts for your team to investigate and remediate. Aryon operates before deployment. It interceptschanges at the point they're made and blocks policy violations before theyreach production. The result: no exposure window, no remediation backlog, and no breach risk from the configuration in question. https://www.aryon.security/how-it-works
Will Aryon slowdown our engineering teams?
No. Aryon includes Policy Impact Assessment, a simulation mode that lets security and engineering teams preview exactly which actions a given policy would block, before enforcement is enabled. Teams tune policies in simulation until they're confident, then activate enforcement. Security gets enforced; deploymentvelocity is preserved.
We use Terraform, ClickOps, and third-party tools. Does Aryon cover all of that?
Yes. Aryon's enforcement layer is source-agnostic. It intercepts changes regardless of whether they originate from IaC templates, direct console actions, CLI commands, or third-party automation tools. This is the coverage gap that pipeline-only shift-left tools leave open, and the exact gap Aryon was built to close.
Does Aryon require agents or access to sensitive data?
No. Aryon enforces policy on deployment actions only. It requires no agents running inside your environment and accesses no sensitive runtime data or existing cloud resources. Enforcement is applied at the change layer, not the infrastructure layer.
What compliance frameworks does Aryon support?
Aryon’s policy marketplace includes CIS Cloud Benchmarks, NIST, PCI-DSS, HIPAA, and NYDFS Cybersecurity Regulation (23 NYCRR 500), alongside AI-generated custom policies calibrated to your organization’s specific risk profile and regulatory environment.
How does Aryon handle policy exceptions without creating security gaps?
Aryon includes a built-in waiver mechanism that allows teams to bypass a policy when genuinely necessary, but never silently. Every exception goes through a managed, auditable approval process integrated into the organization's existing workflows. The result: flexibility without blind spots, and a full audit trail for compliance purposes.
Can Aryon detect drift in existing cloud environments, or only prevent new misconfigurations?
Both. While Aryon's primary function is preventing misconfigurations at the point of deployment, it also provides automated drift detection, identifying when live cloud resources deviate from defined policy over time. This gives security teams full control and tracking over what's in their cloud, not just what's going into it.
Does Aryon replace our existing security tools, or work alongside them?
Aryon is designed to complement your existing stack, not replace it. It operates at the deployment layer, a control point that CSPMs, vulnerability scanners, and SIEM tools don't cover. Your detection and monitoring tools remain in place; Aryon simply ensures fewer risks ever reach the environment those tools are watching.
Is Aryon available through cloud marketplaces like AWS?
Yes. Aryon is available on the AWS Marketplace, allowing organizations to procure and deploy the platform through their existing AWS billing and procurement workflows. This simplifies vendor management and can count toward existing AWS spend commitments.
How does Aryon handle M&A scenarios, where acquired companies bring unknown cloud configurations?
M&A is one of the highest-risk cloud security scenarios, an acquired entity's cloud environment may carry years of undocumented misconfigurations, legacy policies, and shadow IT. Aryon's enforcement layer extends to cover these environments without requiring the acquired organization to change how it manages its cloud. Policies can be applied gradually and precisely, giving security teams visibility and control during integration without disrupting business operations.


